Last time on Dragon Ball Super — Hold on!
That’s not my story.
In my last rambler— Don’that sound like a car? “She drives a Jeep Rambler”, right? So where was I, oh…
Design.
It was something about LCDs and 1U servers, to be continued, and sound effect. Give or take. So this is continuing it.
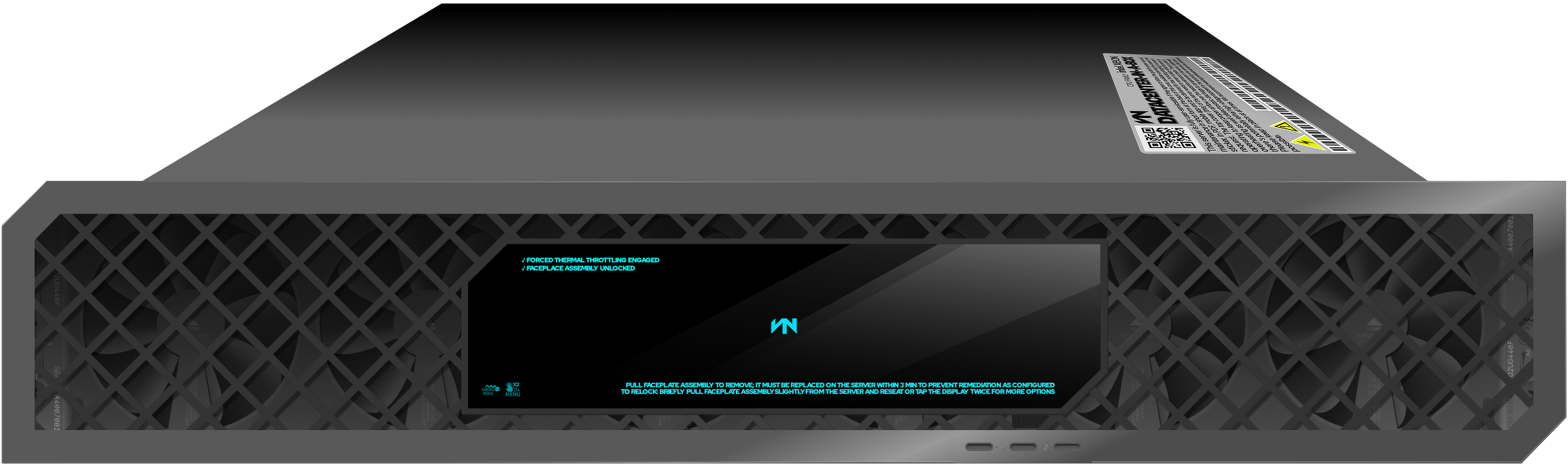
At 144 layers, this was my next attempt on designing a wireframe-(read:-simple-lines-one-color-icon)-looking server.
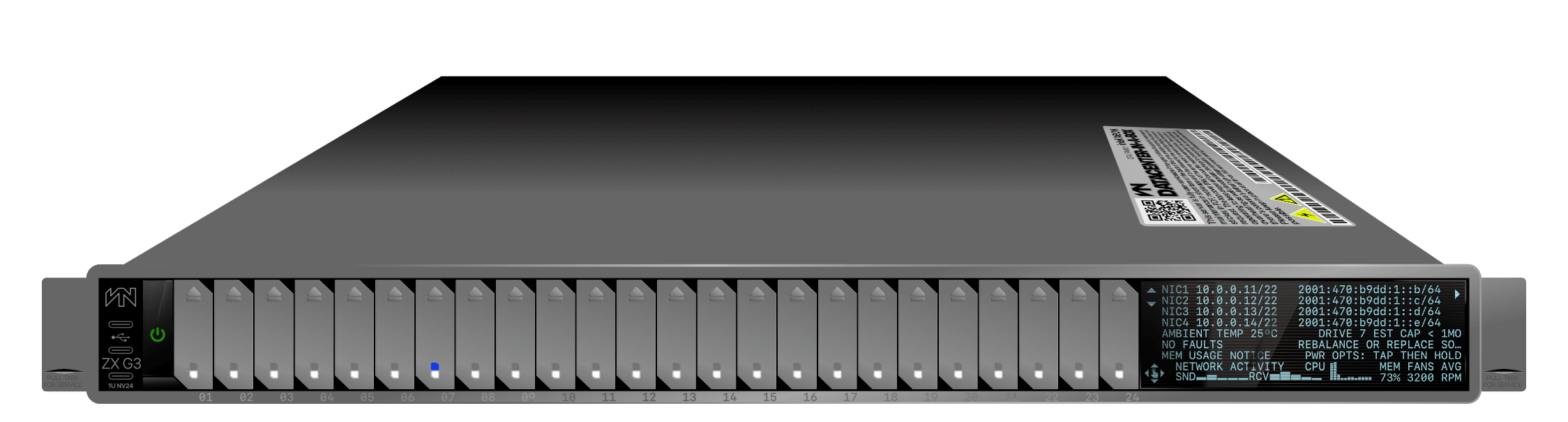
I spent maybe a bit too much time drawing contrasting borders the supposedly wireframe thing so it would be usable on any background, and at the same time tried to blend colors so the border of these borders I drew wouldn’t be noticeable that at some it started looking like fake photorealistic or something. So I just ran with it. The hardest part to make was the sticker on top.
It has a couple of new effects that I wasn’t sure I was going to get correctly: the first is the numbers below the drive slots, which is the same effect on the footer of the site when two gradients with “inverted polarity,” is the best way I can explain it, almost intercept the same color at the same distance but y’know don’t, because otherwise if both have the same color at the same time text wouldn’t be visible.
It’s very simple but it creates sort of an effect of laser-etcher aluminum or some other metal.
If you’re like “beesh, wha?”, probably this isn’t make much sense maybe, huh? See:
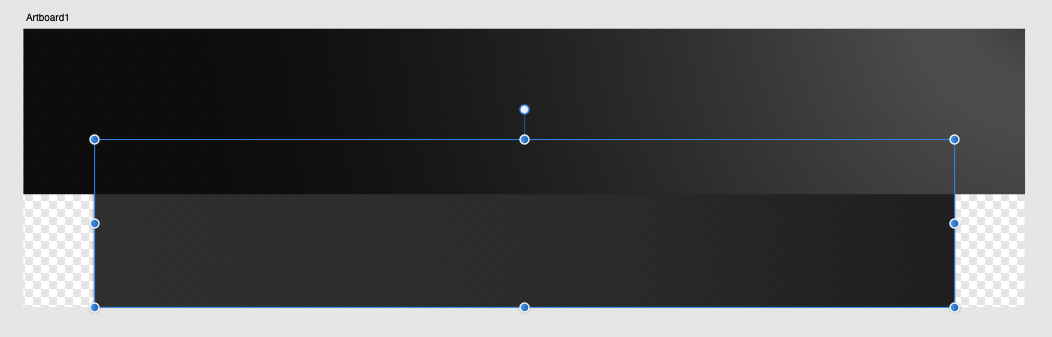
You should see two smooth grayscale gradients in opposing directions, if your display is incapable of showing the image, you’ll likely see solid jagged bands in a handful of shades of gray instead.
It look fucking awesome, much better than the 5s, with full black face, instead of the hideous black square (the display) framed in white in non-dark iPhones had, before Apple finally learned that looks cheap and tacky, unfortunately it took a decade it a decade to get there.T he hot pink shell also was made of aluminum with the little black RF windows those iPhones had in the back and the gorgeous light-catching chamfered edges. I have pictures of it but I zipped them all up and put them on a server, fed up that all people seemed to be taking pictures anymore was for putting them on Facebook and have somebody like them — by the way, if you’re new here Imma be chasing so many tangents it’ll make your head hurt. Seriously, this could be stressful for some people, maybe you should go to another site. There’s no Twitter anymore, this is my space to vent. My HVAC. I have ADHD+OCPD too and the house’s dyslexia for appetizer, be warned — I had an Instagram account way before it was known. I had like 11 pictures because I don’t take pictures of food (when it’s not funny) or selfies. I hate selfies, specially mirror selfies. They’re the epitome of shallowness, I think. There are exceptions to the rule though; dickpics are okay. I mean yours, I don’t take those either, well… not to send them. I grew up at the same time digital cameras and the Internet were also growing up, back when the rules were first being established. That, and I had a very vindictive and bored ex, so I learned fast not to do that. We became made up, became friends, started doing drugs and fucking our other friends together, it worked out in the end, but no pictures. That said, if you feel like sharing and I’d be more than happy to admire your “artwork”. I may even congratulate you, thank you, or put up score cards depending on the day, I will definitely not #metoo you or anything like that. Safe space. “Your cock is my cock,” or how was it?
The other effect is the… um… Remember the iPhone 5 but really more the iPhone 5s? This effect I’m referring to was substantially more pronounced in the 5s, its [very fragile] aluminum case had chamfered edges that caught the light beautifully. When I upgraded from the 5 to the 5s — sidenote: remember when newer iPhones were upgrades? That’s stopped being true around the iPhone XS, …Xs? Who cares — I ordered on eBay for about 10 dollars (USD) a hot pink shell for my old iPhone 5.See? There’s obviously a little more put into it.
The other effect is the… um… Remember the iPhone 5 but really more the iPhone 5s? This effect I’m referring to was substantially more pronounced in the 5s, its [very fragile] aluminum case had chamfered edges that caught the light beautifully. When I upgraded from the 5 to the 5s — sidenote: remember when newer iPhones were upgrades? That’s stopped being true around the iPhone XS, …Xs? Who cares — I ordered on eBay for about 10 dollars (USD) a hot pink shell for my old iPhone 5.See? There’s obviously a little more put into it.
It look fucking awesome, much better than the 5s, with full black face, instead of the hideous black square (the display) framed in white in non-dark iPhones had, before Apple finally learned that looks cheap and tacky, unfortunately it took a decade it a decade to get there.T he hot pink shell also was made of aluminum with the little black RF windows those iPhones had in the back and the gorgeous light-catching chamfered edges. I have pictures of it but I zipped them all up and put them on a server, fed up that all people seemed to be taking pictures anymore was for putting them on Facebook and have somebody like them — by the way, if you’re new here Imma be chasing so many tangents it’ll make your head hurt. Seriously, this could be stressful for some people, maybe you should go to another site. There’s no Twitter anymore, this is my space to vent. My HVAC. I have ADHD+OCPD too and the house’s dyslexia for appetizer, be warned — I had an Instagram account way before it was known. I had like 11 pictures because I don’t take pictures of food (when it’s not funny) or selfies. I hate selfies, specially mirror selfies. They’re the epitome of shallowness, I think. There are exceptions to the rule though; dickpics are okay. I mean yours, I don’t take those either, well… not to send them. I grew up at the same time digital cameras and the Internet were also growing up, back when the rules were first being established. That, and I had a very vindictive and bored ex, so I learned fast not to do that. We became made up, became friends, started doing drugs and fucking our other friends together, it worked out in the end, but no pictures. That said, if you feel like sharing and I’d be more than happy to admire your “artwork”. I may even congratulate you, thank you, or put up score cards depending on the day, I will definitely not #metoo you or anything like that. Safe space. “Your cock is my cock,” or how was it?
At 470+ layers…
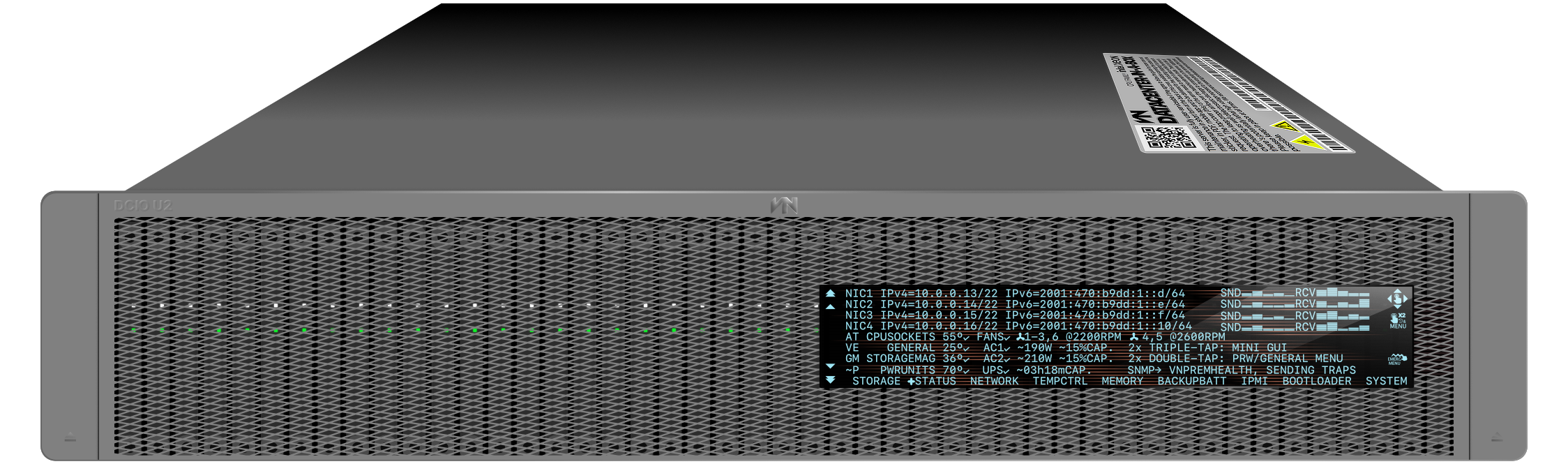
Is that thing above. The list of layers is massive but it’s organized in groups so it’s manageable. The need for that organization gave me the next idea:

You can disassemble it !
Above is with the grill and rack mount ears’ covers removed. Below, with the display removed, leaving only its support arm and rainbow cable, I don’t know how I’m only now catching that detail.
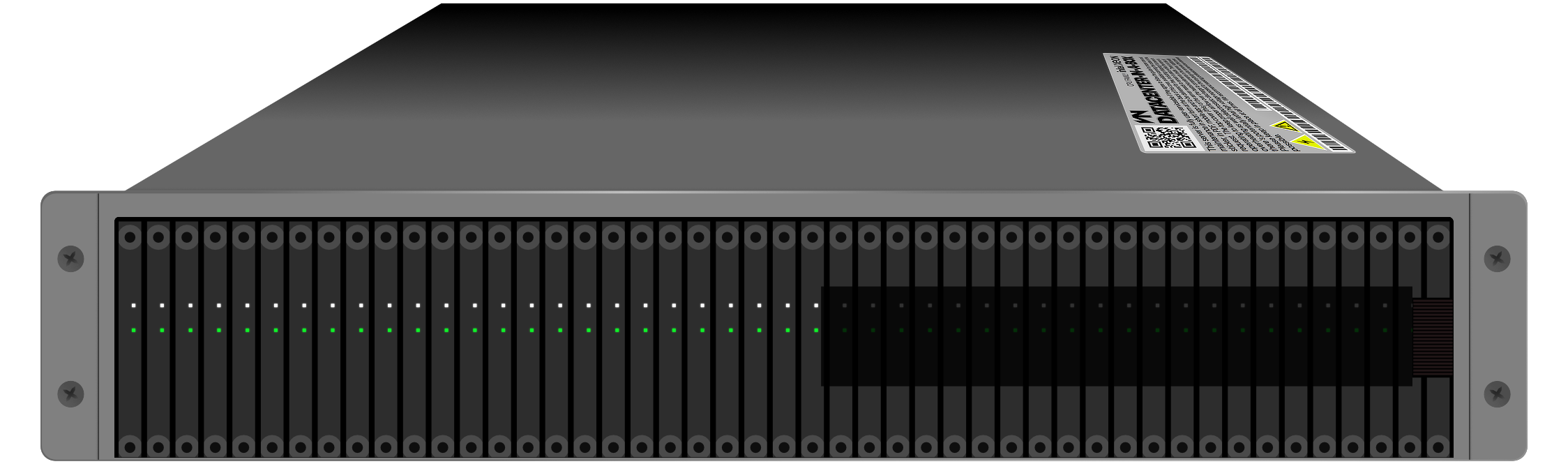
Rack mount ears removed:
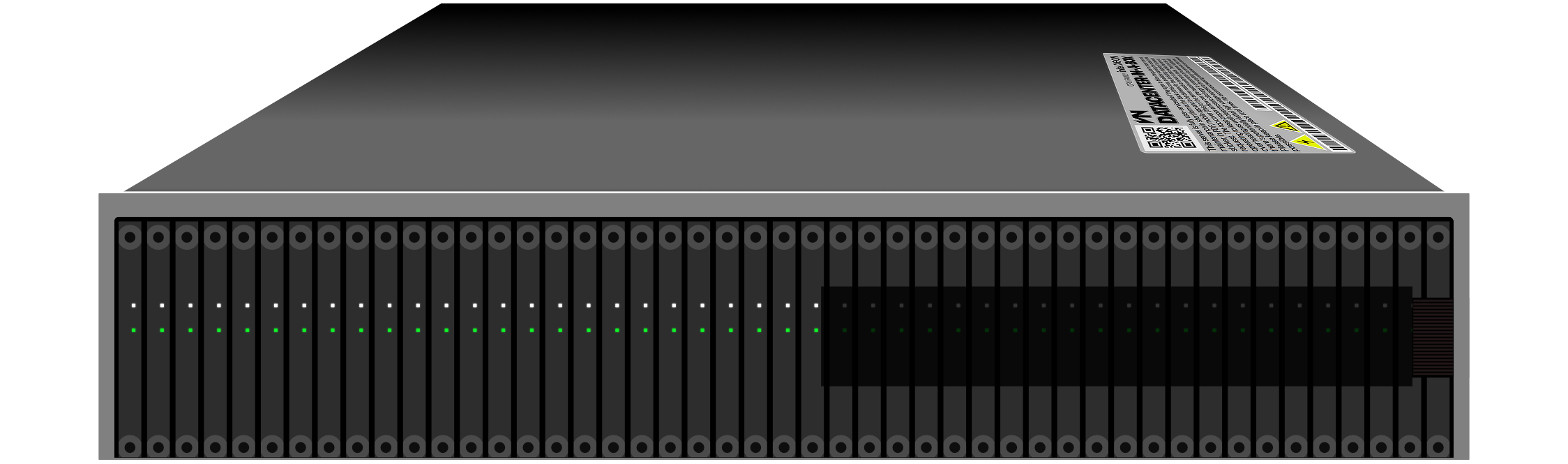
Display assembly support arm removed:
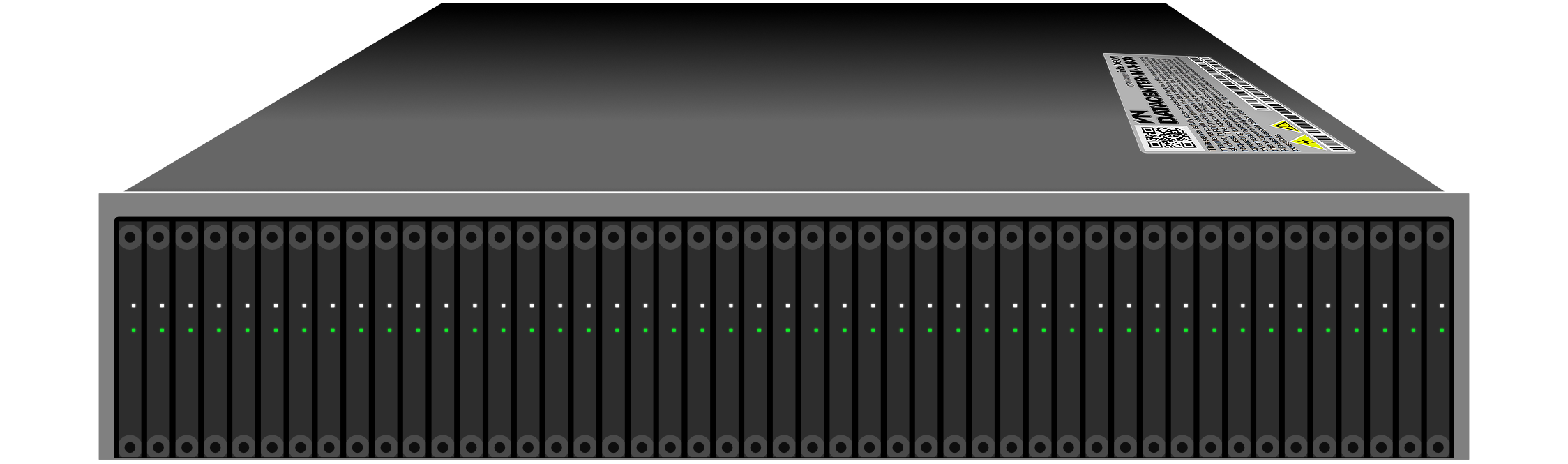
Disks removed:
And yes, I’m recycling the top cover and will continue to recycle for as long as it matches because it was sooo annoying to make. I hate it.
While doing a network map to ask for assistance in some forum, I made some shapes to depict routers and what not. I did this trapezoidal rectangles so they’d fit a word inside for the network map they were supposed to represent.
Next thing I knew I had drawn 1121 layers, well, not all at once. I tweaked a few things some days later.
This is G3 (borrowing from HPE ProLiant servers,) it disassembles as well, but it doesn’t have as many layers in that way:
Above, fully assembled. Like in the previous one, the display is a capacitive touch screen. I mean, if I’m gonna make believe, I’m gonna go all out, right?
That said, it’s still a monocromatic OLED display. There are certain gestures that you do during booting to enter boot selection and shit like that, I thought a lot about this and made designs only to support this image where it’s not even visible.
Hmm… I have issues.
If you remove the display, the fan assembly is exposed. The server is not supposed to stop. Proximity sensors slow down each of the fans as you get closer to them. Touch the center to arrest it. Push the center to release the fans from the spring-loading mechanism:
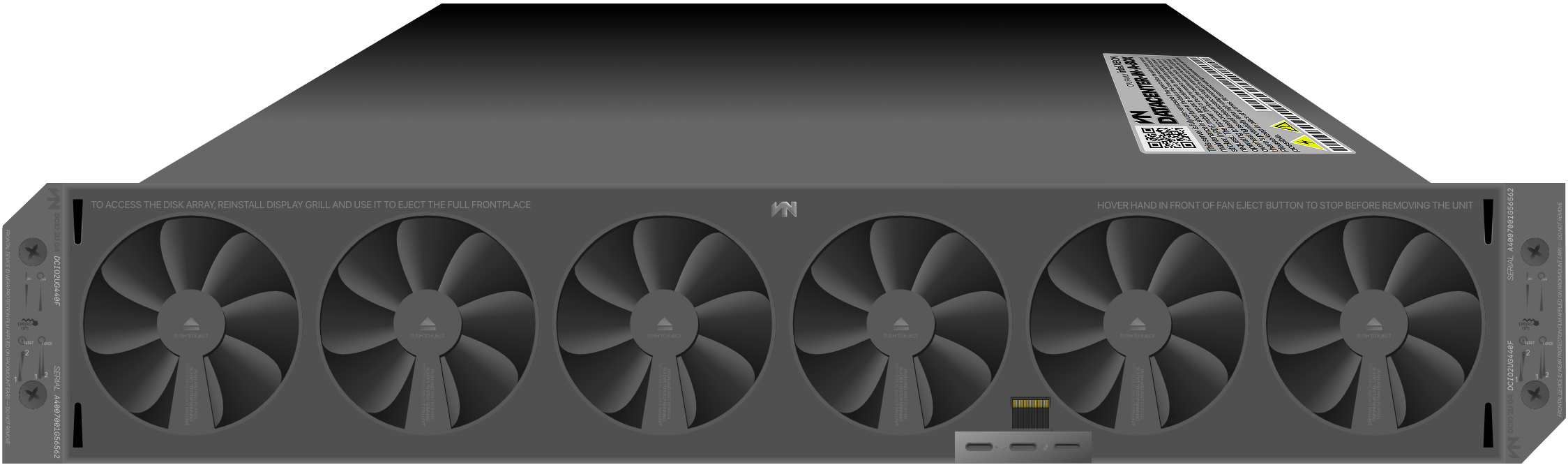
Something very expensive to make would be that the disk lay behind the fans, not the other way around. I mean, it keeps the disks cool and looks badass, don’t it? Plus, for me, it’s free to make; I have the wannabe-designer’s discount.
There’s a second display inside, but it’s not a real display, but it’s like that edged glass or acrylic that it’s lit from out of sight and things one it appear like holograms floating. I’m sure you know what I’m talking about. Hey, don’t look at me. They blew all of the budget in a hot-swapping disk magazine behind the fan assembly.
Do you know how fucking expensive that must be?
Oh yeah, I forgot, while the server is on you are supposed to indicate in the front display or remotely that you will swap a disk, it starts ramps up the fans, and starts lightly throttling the load so things cool inside, that way you have like a minute or two to swap a disk while the fans are removed. Of course there would be at least two more fans inside or in the back in the power supplies.

That’s it. No more layers. Noticed the USB ports, BTW?
I could’ve removed them but servers from some reason no matter how advanced they are, they have always one compromise like that, a fixed front I/O assembly that leave a square hole in just off-center to the left of the front grill.
It was kind of annoying to make because I had to design all layers about that flaw.
In the fan assembly, if you look closely, there’s a rainbow cable and exposed contact port for the display that is locked in in this piece.
There’s one more, or two, IDK. Maybe later.