In modern TR-069-fied CPEs (Customer Premises Equipment) this involves several steps, most of it is preparation.
TLDR
If you already have the device in bridge mode and you are only trying to figure out how to do IPoE skip to 3.2, or if already sorted that out too and you’re looking for how to keep the connection from going offline 3.2.2.
Table of contents
- TLDR
- Table of contents
- 1. Recon
- 2. Redo
- Preemptive tips
- 3. Rework
- 3.1 PPPoE
- 3.1.1 MSS Clamping
- 3.2 IPoE
- 3.2.1 WTF is IPoE?
- 3.2.2 [Re-]Authentication
- 3.2.3 Lorem ipsum dicpic das un (that’s French for “let’s finish this”, I heard in a lie I told)
- 3.1 PPPoE
AD SPACE
ESPAÑOL? (do you like taquitos?)
La versión original de esta página era de hecho en español. Está enfocada al proveedor mexicano Megacable (servicio de fibra) en su mayor parte, pero no hay razón por la que no se pueda aplicar a similares.
And if we bye-bye and VyOS that firewall?
If you’re comfortable in the CLI, this might be a great time to check out VyOS. It’s among the best firewall/routing platforms I’ve tried, it’s blazing fast. Although personally I haven’t checked it out yet but there’s a high chance it’s got a fix for this already, considering it has an IPoE server out of the box. I kept my most recent VyOS firewall and I already starting the switch back to it to test this. I’ll update this post if there’s unusual that you’d do on a “regular” DHCP WAN uplink. Also good are CHR from Mikrotik (a perpetually1 licensed virtualized version of its RouterOS routing platform starting at about USD50,) and a bit bloated and slower but still good, OPNsense which like VyOS and pfSense, has professional support options too.
1. Recon
- Reset the ISP-loaned toaster to its defaults using the little pin hole or what-have-you.
- If you have admin access printed in the box, log in.
- If you have one of those ISPs that requires you to have their blessing to get “admin access,” you’ll have to dial the number and put up with the condescending questionnaire in order to get those credentials. Remember they might expire so log in right away.
- The CPE uses profiles for the connection, they’re not called that but probably something more confusing or mistranslated. Several profiles at once might be configured but only one is online. Unless it only handles one stack (i.e. IPv4, IPv6), then two. Locate the active one, expand it if no already and note down the settings so you can create your own profile after. Some key points:
- A profile will have a series of checkboxes for “Service Type”. The options will be something like: Internet, Voice, Other, TR-069, IPTV
- When you create your own, you only need — and should only select — “Internet”.
- A profile will have a series of checkboxes for “Service Type”. The options will be something like: Internet, Voice, Other, TR-069, IPTV
- It will have the authentication type, normally PPPoE or IPoE. The latter could be named just DHCP, or “dynamic”. If it’s PPPoE, you should know the username, and password. Basically the most important thing to learn from here is the authentication type, also called connection type (not so much the credentials,) and the WAN-side VLAN the servers you need to contact reside on.
- For older DSL types, take note of the VPI and VCI values. This will be really rare in modern-ish networks though. If you see these values, you won’t see/need the VLAN value.
- Next, find out your WAN-side MAC address, it should be on the status page for Internet, WAN, or even the ONT/OLT link details page.
- If you are replacing or have replaced your fiber ONT, in the ONT/OLT link details/status page, find out what serial number your ONT is using. If it needs a password, see if you can get it from the UI, otherwise you will have to phone support. Sometimes it’s just a mistakenly entered password we ourselves entered that’s not even considered to accept the ONT registration with the OLT.
2. Redo
Start by finding the TR-069 section on disable it. Hopefully your ISP doesn’t have fail safes for it to be re-enabled on its own, but let’s face it; that admin access account, is not a root account. You are powerless until you get your own ONT/modem.
2.1 Two point one and CPE tips
Set up a static address on your computer on the same subnet of the CPE in preparation for bridge mode, some really crappy CPEs still lose all access upon enabling bridge mode, but most simply turn off DHCP.
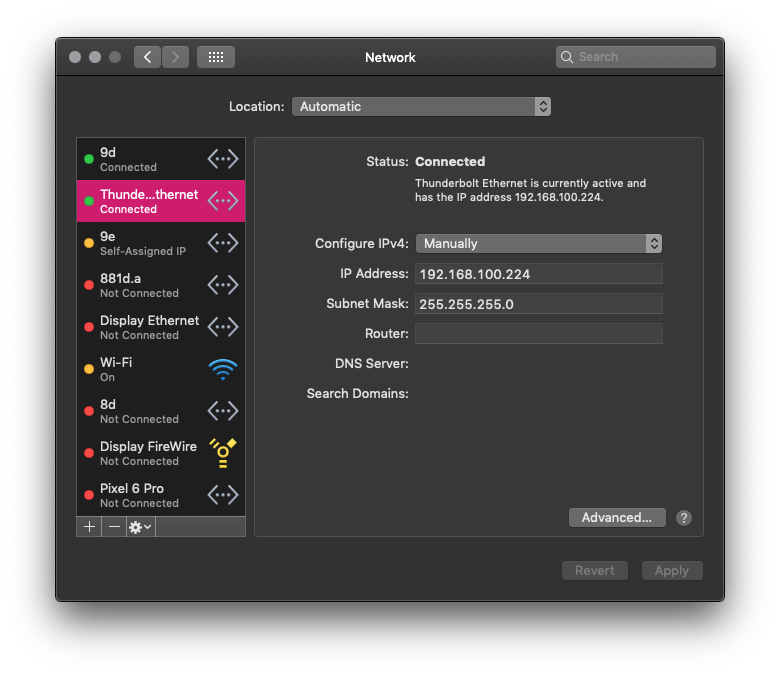
You don’t need a full network config. In the picture, the interface is configured with lower priority so the main interface (a VLAN in this case) still allows Internet access for whatever that might come up.
Additionally, it’s imperative to use plenty of lube but not too much that it gets sloppy. Sure, it’s unrelated but it never hurts to know. You know what hurts though? No lube! Back to subject.
You will have to learn and adapt. That means, pay attention to the order of the steps as you take them, if it locks you out at a given step, then next time leave it for the end. Always wait a little to see the outcome, the CPE might have an config auto-revert if the connection with your browser is lost for too long, or it may have a confirmation step. Watch the lights on the CPE, identify the pattern of normal operation. At the same time, don’t wait for too long because the session will expire due to inactivity, or because it has a hard limit. Knowing how shortsighted ISPs are, it will be most likely the latter.
Open private sessions on the browser, each window is a new session whereas in normal browsing all windows are your current session. It really depends on how well the site is put together, don’t expect miracles and don’t close the original window even if you get an error page. You can at least use it to get the history of addresses where settings are on the CPE. Probe often the CPE from other sessions after you applied some change and it started taking a little too long to respond; if it takes long to respond in another session as well, it means it’s working on it. Do it carefully. The bad code in these cheap devices might make them crash when overtaxed. On the other hand, if it responds right away it means that it probably has already applied the changes but, also due to bad code, it failed to acknowledge it. Double check just in case, navigate to another page and back. Keep the dev tools open of your browser with the option to disable cache enabled.
If you get locked out due to too many invalid password attempts, change the static IP address of your system and open a new private session.
This is the part where bridge mode is set in the CPE.
- Delete all WAN profiles
- Create your own WAN with the settings you gathered, except:
- Set it on bridge mode (rather than choosing PPPoE, IPoE, static, dynamic, …)
- Bind it (bridge it) to all LAN ports or just the one connected to your firewall, your call.
- Don’t forget the VLAN.
2.1 Disable extras
Now it’s time to do a little housecleaning on your CPE, especially if it’s the kind that will rotate its credentials.
Go to the Wi-Fi settings and turn it off. Turn everything off. Since you won’t be using it, it’s only creating interference for yourself and others. Then navigate through all pages and turn off everything that you can turn off: all firewall “protections,” all access controls, UPnP, built-in media servers. Everything must go. You want all limited resources bridging traffic period.
“But the firewall too?”
Yes. What do you think it’s going to happen if the device has no routable address?
“But what if somebody in the ISP’s internal network… since it’s layer 2 on that side, ain’t it?”
Yes, and no. Yes, young padawan, it’s usually layer 2 on the WAN side, hence why you bridge to it, but that doesn’t mean you’re with other customers in the same broadcast domain. WAN side switching is a bit different than LAN-, or even ultra-badass datacenter TOR switching, or other LAN fabric. ISPs need no MAC addresses or packet/frames headers to direct traffic. They use locally significant connection identifiers over a fixed path. These fixed path constructs are called switched virtual circuits when set by a signaling protocol or permanent virtual circuits when set manually. They create a logical association of two endpoints, which can make it as if there was nothing else in the network—if I remember correctly. Point is, I’m really digging in within the deepest of my geek reserves (and depleting them, I’m gonna need to read book or cereal box after this) to come up with this lame half answer. Just take it.
If that doesn’t convince you, remember that you are setting up your own firewall, even if ISP-loaned panini maker gets compromised; whatever, it’s out of your perimeter.
3. Rework
Now you only need to adapt and apply the rest of the settings to an interface in your firewall. This should be easiest, and — if you use IPoE — the most important part.
3.1 PPPoE
For PPPoE, I need to explain nothing. However…
3.1.1 MSS clamping
I do recommend that you set MSS clamping though. If you’re handling both IPv6 and IPv4 on the same interface, set the value at the most to 1432. Depending on your ISP it might be even less. If it’s only handling IPv4, set it for 1452 at the most. Start using this value network wide, it’ll avoid so many issues.
Just as a refresher:
| IPv4 | IPv6 | HE Tunnelbroker IPv6 | |
|---|---|---|---|
| Packet size on the Internet | 1500 | 1500 | 1500 |
| PPPoE header | 8 | 8 | 8 |
| IPv4 header | 20 | 20 | |
| IPv6 header (covers IPv4, unless in IPv4) | 40 | 40 | |
| TCP header | 20 | 20 | 20 |
| Remaining for payload | 1452 | 1432 | 1412 |
On the ‘senses2, this is done in the interface config. Just below you select what kind of interface it will be and below MTU (which is best to leave blank unless you really know what you’re doing)… like really really.
Note that MSS will always be lower than MTU. That doesn’t mean that if you set MTU the other is limited automatically. Some firewalls might, but don’t expect it. MSS clamping is an aid, it happens as a conversation between the firewall and a another TCP endpoint. MTU thought it happens to be mentioned in machine-to-machine conversation as well, it might just, y’know…not. It’s a hard limit, well sort of, it auto-adjusts in many cases but I don’t know the specifics. Sorry! One last thing, pinging itself uses the ICMP protocol, with overhead of 8 bytes. During ping it’s not counted but when ping exits, it add them back to the report printed.
3.2 IPoE
3.2.1 WTF is IPoE
When I first read about IPoE, I was “IP over Ethernet, hmm… Sounds like something that was already happening, right? Oh well.” but as I learned a little more about it, namely that IPoE is an authentication method that uses MAC addresses to assign IP addresses… “Seriously!?— What is wrong with these people!”
But as it turns out is more advanced than DHCP it seems (it’s not).
It’s basically a glorified DHCP server that may or may not have (it never has) TLS extensions. What for? Who cares. The thing you need to know is that when you set a client, or rather WAN interface in a firewall platform that has no specific IPoE option, you need to use DHCP. That will be a lot of them because only CPEs, which are cheap and what we’re trying to replace, have the IPoE option.
This is necessary regardless if you have a static IP address, during the last steps of DHCP’s DORA or what’s-her-name, the request is what’s used as trigger for authentication, then with the acknowledgement comes the authorization and then the client is allowed to exchange data.
You’re not done yet though.
3.2.2 [Re-]Authentication
Since the DHCP address leasing process serves as the authentication/authorization mechanism, you sort of need to do it all over again before authorization expires, likely before the lease. Normally DHCP checks (refreshes) with the server when half of the lease is up. If the server doesn’t answer, then halves the time again so at ¾ the lease checks again, rinse and repeat until finally it releases the lease if the server failed to pick up.
I wasn’t planning on bothering with detail, but this thing is for myself as well, it’s my personal3 notes if you will, and I’d hate not knowing, on top of that I must’ve stumbled into a version of the RFC “for dummies” because it was very straightforward to understand. Like a dangling **** in my face, I seized it.
The DHCP message for both requesting and refreshing (extending) an lease is the same one, DHCPREQUEST, I’m not kidding, I went to investigate and I just came back all the way from the farthest tab to the → (I think that’s right according to the shoulder buttons on my Nintendo.)
DHCPREQUEST is actually used in four different occasions. Let’s just focus on the two involved.
DHCPREQUEST / SELECTING
The client may catch a few DHCPOFFER messages and select the best offer. If nothing is suitable, it might send another DHCPDISCOVER message, blah-blah… This DHCPREQUEST is a broadcast message, it must include the server’s IP address, it must include the requested IP address, and not include the client’s IP address.
DHCPREQUEST / RENEWING
The client maintains two times, T1 and T2, that specify the times at which the client tries to extend its lease on its network address…blah-blah… At time T1 the client moves to RENEWING state and sends (via unicast) a DHCPREQUEST message to the server to extend its lease. The client sets the ciaddr (its own address) in the request, and must not include the server’s address nor the requested address.
In summary:
DHCPREQUEST during… | SELECTING | RENEWING |
|---|---|---|
| Transmission type | broadcast | unicast |
| Includes server’s address? | ✔︎ | ✖︎ |
| Includes requested address? | ✔︎ | ✖︎ |
| Includes client’s address? | ✖︎ | ✔︎ |
That process doesn’t seem to be quite enough for authorization to happen though. During testing, although with only one ISP, what has been observed is that the client will eventually lose authorization but it won’t be until the lease is up (which is longer than the authorized time) and starts what’s-her-name all over again become authorized again. This is not too different from restarting the interface.
And indeed it worked. The regular process of address renewal just doesn’t cut it to authorize the client in IPoE. Restarting the interface would will reauthorize the client right away.
The problem is that if you have a dynamic IP address, the change of it would mean routing tables need to be flushed, connection states need to be cleared, which would then force connections to be reestablished. It’s a noticeable hiccup in the network. Not a big deal for humans, but what if you have big non-resumable transfers in progress? And by you, I mean you as a server, since I assume if you’re doing all of this you might be self-hosting something, which if you do, it means you’re likely not bandwidth-constrained, but what about your clients4 though?
There is one way that seemed to be working flawlessly in triggering the DHCPDISCOVER in order to get to the DHCPREQUEST/SELECTING, without restarting the interface: bringing the interface up when it’s already up (without bringing it down first.)
As I mentioned one or two dozen times, I have a static IP address to test with only. I’m always getting the same address even if it needs to be requested as a dynamic assignment, therefore there’s not flushing or clearing of anything, and not all DHCP servers rotate their addresses right away, in my experience with them, they’d usually re-offer the same address if the lease is still valid and the client never released it.
I had always had PPPoE before, from ADSL all the way to VDSL2 and GPON, I’ve always used bridge mode. This IPoE stuff was foreign territory. The service would cut off every day at about the same time if the interface wasn’t restarted, it would just be continue playing dead.
It wasn’t really a mystery of what would work because the ISP used to be a cable provider (coax) before all of them converted to fiber, I’ve heard/read that spoofing the MAC address is common practice with cable and that generally cable uses DHCP so I could put two and two together.
However, because of that stupid static address, I wanted to make sure there was absolutely no chance of setting it up manually before bending over and praise the lord.
And to really really really make sure I covered all bases, I ordered my own ONT a repeated everything I had tried so far. You know how the saying goes “keep your enemies close and the lube closer” or something like that.
The thing is, on IPoE, there’s no session monitoring. If you got authorization earlier and your [spoofed] MAC address matches, as well as your [also spoofed] ONT serial number, all will work if you set it to manual because you’re already authorized. I kinda thought that would happen but the only way to confirm was waiting a day. When eventually authorization expires at which point you’ll end up offline and with absolute no chances of reconnecting since DHCP is not happening.
I’m intentionally making mistakes so you don’t have to. It’s really so I don’t have to but it doesn’t sound as altruistic.
If you do have a static address, beware of false positives successes
Now, for something useful.
3.2.3 Lorem ipsum dicpic das un (that’s French for “let’s finish this”, I heard in a lie I told)
If you’re using OpenWRT, the solution to this is to set a cron job to bring up the interface constantly. In the scenario I had to test, I will always get the same address. There’s no disruption, if there even is supposed to be some, setting it for an hour ended all problems.
In LuCI, the GUI for OpenWRT, in System→Startup→Local Startup
*/60 * * * * /sbin/ifup local4
You might not have an environment when cron jobs are executed. You can’t rely on the PATH, in other words, you must enter the path in full.
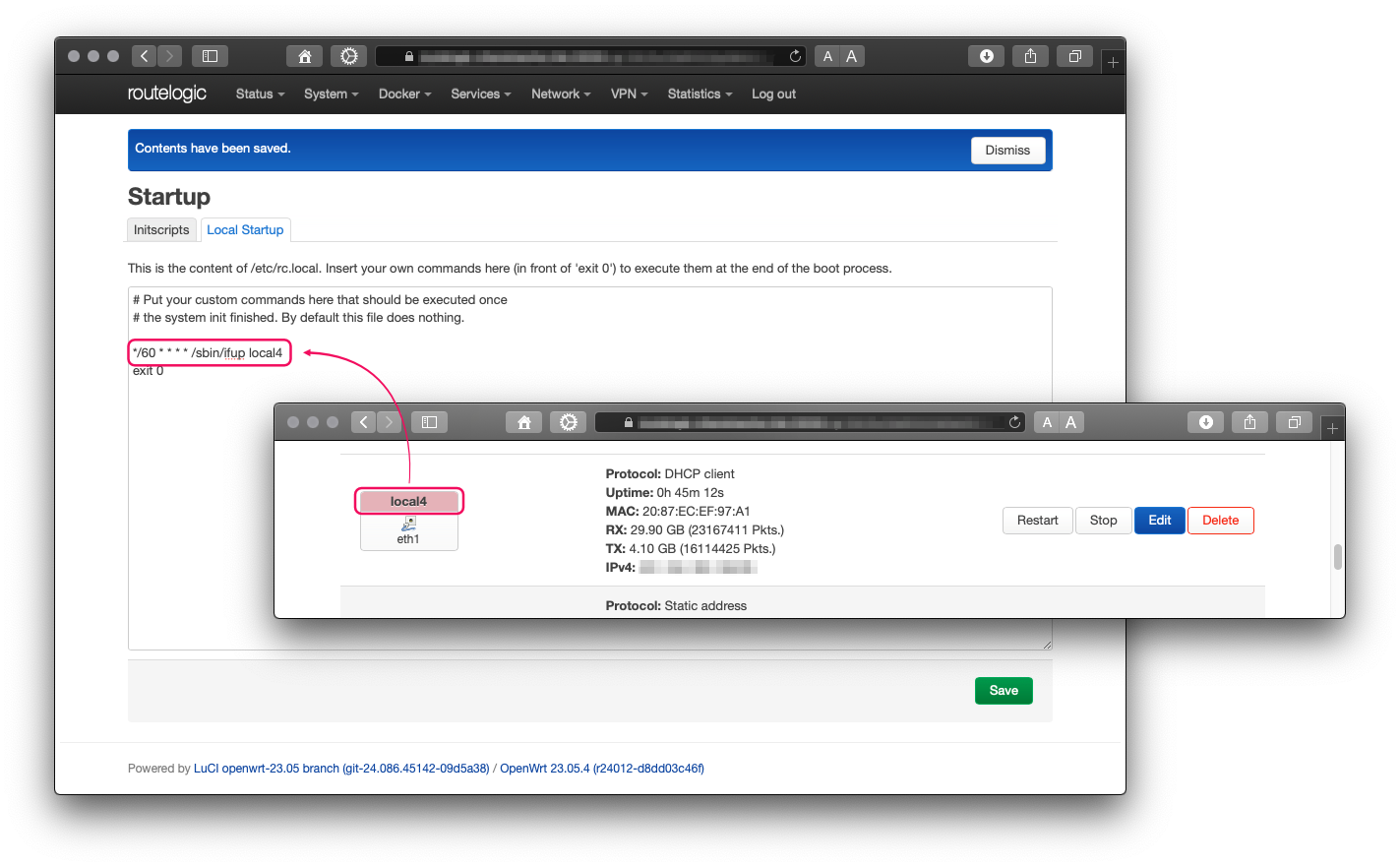
The interface names is what you set it to be in the config, not the BSD-ish one.
Which BTW, you can get with: ip link | grep -Ei '^\d+:.*' | awk '{print $2}' | grep -Eo "(\w|.|\d|\@)+" — again, not for the ones you actually need, just a tip.
And as always to find the location of a program use which:
which ifup → /sbin/ifup
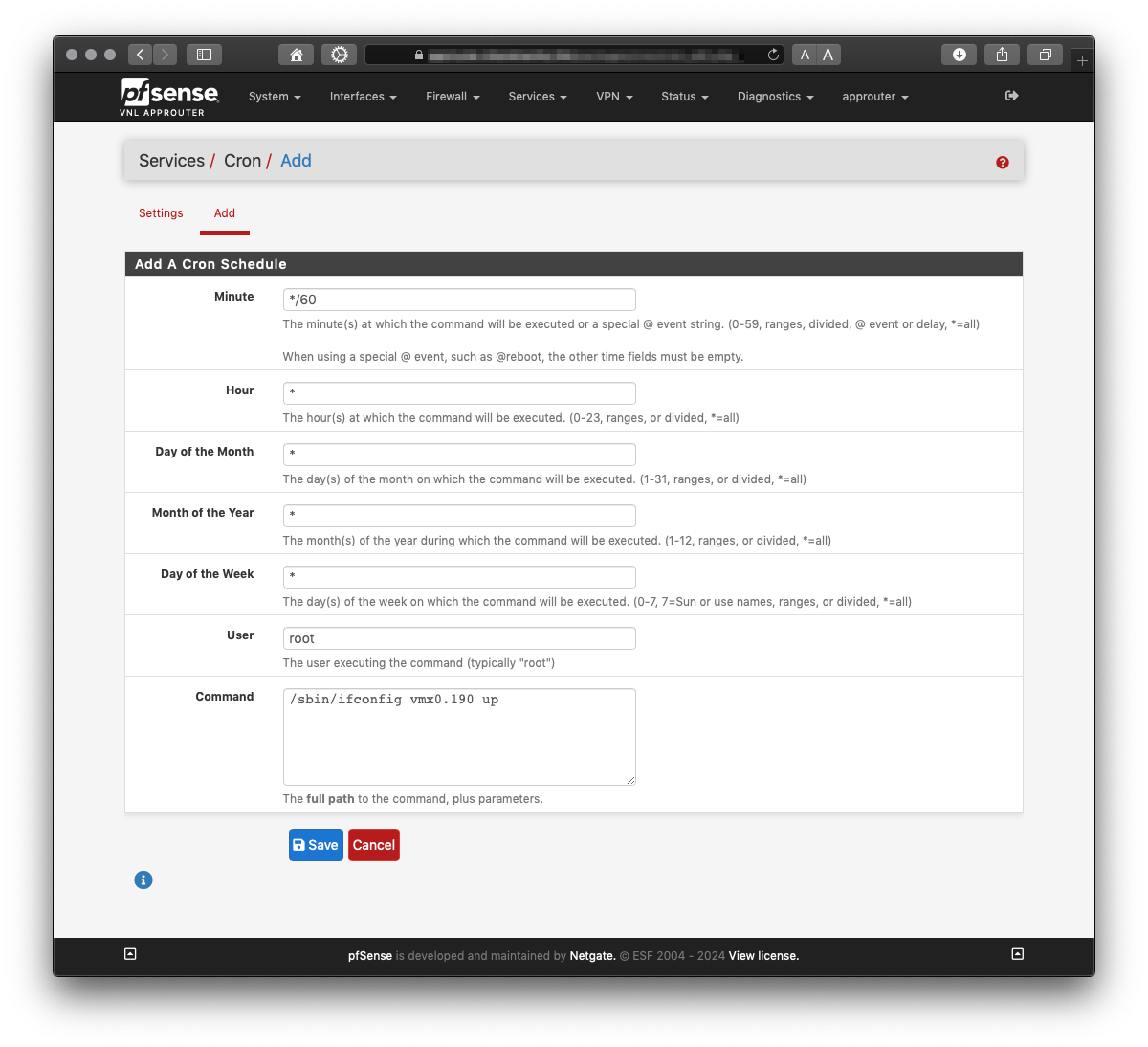
On pfSense you’ll need to get the cron package if you don’t have it already.
pkg install -y pfSense-pkg-Cron from the CLI should do it.
There’s no ifup in pfSense’s xBSD. So, next best thing:
which ifconfig → /sbin/ifconfig
List interfaces:
ifconfig | grep -Eio '^(\w|.|\d)+'
Build command:
*/60 * * * * /sbin/ifconfig vmx.190 up
And now you’re done. Kinda… you still need to adjust timing if the re-up is indeed disruptive, you can fast forward to it by setting a really short time to test. If the networks stutters, you’ll have to test how low does your authentication last. The easiest way to do it is by starting a ping to a public DNS server or some other server that won’t flag/block you for abuse or something. Do it before you do a manual interface restart so it’s logged in the ping. Don’t forget to check it from time to time because the sequence restarts after a while.
- I don’t (and I won’t ever) recommend software that expires unless there’s an excruciatingly good reason for it. Convenience is never a reason. ↩︎
- pfSense, OPNsense ↩︎
- except not personal but more or less exactly the opposite: public. ↩︎
- as in visitors, guests, users. HTTP clients, FTP clients, VoIP clients, etc. ↩︎