And by “come with IaaS”1 I really mean “is Google’s customer-provided IaaS. Well… more or less, I’m taking a bit of creative liberty, but I don’t really have to make the same exact infuriating point.
If you’re using one of the more recent Androids (sic,) besides its usual overly-invasive status quo, you may have stumbled into terms like Private Compute Core, Android System Intelligence, Federated Learning, etc.
I don’t remember which of these even goes all the way making the effort of putting up a show (in the settings) of either not needing or forbidding itself from connecting to the Internet (as if it would let you have a say on system-level things anyway) so you’re really confident you’re privacy is being respected.
I’m going to trust Google on this just this once, but mostly because it makes my next point pass as well-researched. (To be honest, I actually “researched” it but finding the ugly was so fast and expected, that it was super anti-climatic…and expected. The lack of build up robbed me from the “Igotchumothafacka!” moment.)
But let’s pretend I’m gonna teach you how to give birth. Hope you did your Hamas course. Yeah, I know that’s not it, but it feels more now, y’know?. Moving on.
Though that private core thing might be allegedly private, it’s meant to interact and carry back and forth data with all other apps on your devices, such as your contacts, location services, calendar, the phone app, etc. And last time I checked, those are under no such fatwa, quite the opposite: the last time I set up what’s currently my phone, every single first party app required me to accept a privacy policy before using it.
BTW, this is a Pixel device, which I got because I thought my previous Xiaomi device was too invasive — Was I about to have a first hand demonstration of what invasive can really be. I had to replace [almost] literally all first party apps with F-Droid-sourced apps. The false belief of having only first party apps would mean a less invasive experience was one of the three reasons I chose this device. It seems as invasive as it was, Xiaomi was actually taming Google’s own egregious efforts not before getting in some of their own, of course.
For example, just moments ago that I mentioned the phone app, it’s not based on nothing. The phone app — which you’d think is the core app of a portable computer device specifically known as a phone — somehow needs from external support to fulfill its reason of existence. No wonder why a little earlier it had been removed from the AOSP. The only app that I didn’t replace is the Settings app.
Which is invasive as well, but it’s the most I can do.
I’m using a custom Android image which already have some privacy protections but it’s not a privacy-focused, BlissRoms, which I thought it was the best featured without being gimmicky since the first time I tried to get it until I finally got it working a full year later. My device is both under MDM and has root access, the bootloader is unlocked. Whenever I’m not using my ultra-filtered Wi-Fi connection, I’m permanently connected to the same network through tunneling so data coming in and out of my device if sifted at all times, except for Google’s of course which has its own rules. I’m a remote code executor’s dream, on the flip side, it gives detailed visibility and manageability into and of my traffic.
I have more trust in what Windows Defender in Windows Server classified as malware than of a Google Play Services connection, and this launcher that’s I use that’s was a premium purchase at some point but now it’s adware2 That changed too BTW, but that’s for another day however since I mentioned iPhone devices (you’re not supposed to say “iPhones” because IDK… stupidity. Though the deeper reason might be so you don’t think as iPhone “devices” as general computing devices that do things like running software from other sources that don’t involve paying Apple for shit.) as stupid as I hear Siri has become, at least it’s something. I miss stupid Siri, I miss any voice assistant so I don’t have to fumble with my phone which is a fucking bezel-less screen with no thought put on how to hold it without activating random things every fucking time. If you want an assistant on Android you have to surrender so much information it should be illegal. On top of that it asks requires you to train your voice in it, or rather train a model of your voice that’s stored not in-device but paired with the first Google account the device get a hold off on and replicate across the globe in Google’s data centers. It’s not because you’re so important that your information needs redundancy, it’s because you are important as a product for Google to sell that your monetizable information (and since what’s not monetizable today could be monetizable tomorrow: everything) needs redundancy.
I miss local universal search also known as Spotlight. Pixel devices now come with a non-optional Google search. What could there be so urgent that needs being searched from my homescreen rather than some setting or thing on the actual device. To be fair, Apple patented Spotlight[‘s functionality] on a phone, that’s why Android devices couldn’t have universal search in the beginning but I think since then that has expired.
Currently, Pixel devices come with zero functionality — that’s none of the advertised (or not) features — that doesn’t need you to accept a privacy agreement or statement or some other waiver (whether bounding or potentially binding) of liability. Why do they need that? Because that’s how legally Google has a head start covering its when for the eventual inevitable lawsuit. But then by then it has collected enough data, and Google seems to be aware that people think shit about it but they’re stuck as evidenced by their continual use of it, so it is unrepentant. That’s what I’ve witness over and over.
By the way, if you’re thinking “you just a paranoid imbecile, I will fuck with you and take one of you famous rimmings, but you’re a moron with too much time to kill.” That’s understandable. I’m not a journalist, I’m not bound by journalistic ethical guidelines or whatever. I would be honored if we fuck each other silly, but I don’t think I’m being paranoid because then I must be imagining — that’s what paranoia is, right? — the Class Action Suit that has currently undergoing trial, the one that I’m a part of; where Google is being sued because even if you set some data collection off, it found some creative way of still getting it under some other pretense, and doubled down on it trying to claim fair game if it confuses it with unclear um, well… everything. See here: https://www.googlewebappactivitylawsuit.com
It’s been creative like that in other ways too, this is the company that secretly CCs (or CCOs) emails to its legal team, department, or whatever so the message enjoys Attorney-Client Privilege and thus, as I understand, in US law it can be potentially blocked from everything and everyone if the company chooses, unless it’s forced to reveal it during the discovery phase of a lawsuit, that is if it didn’t delete it because it’s unlike Google to retain all information about you. Wink emoji. Knowing look. Black woman’s “mm-hm” judgmental perfection.
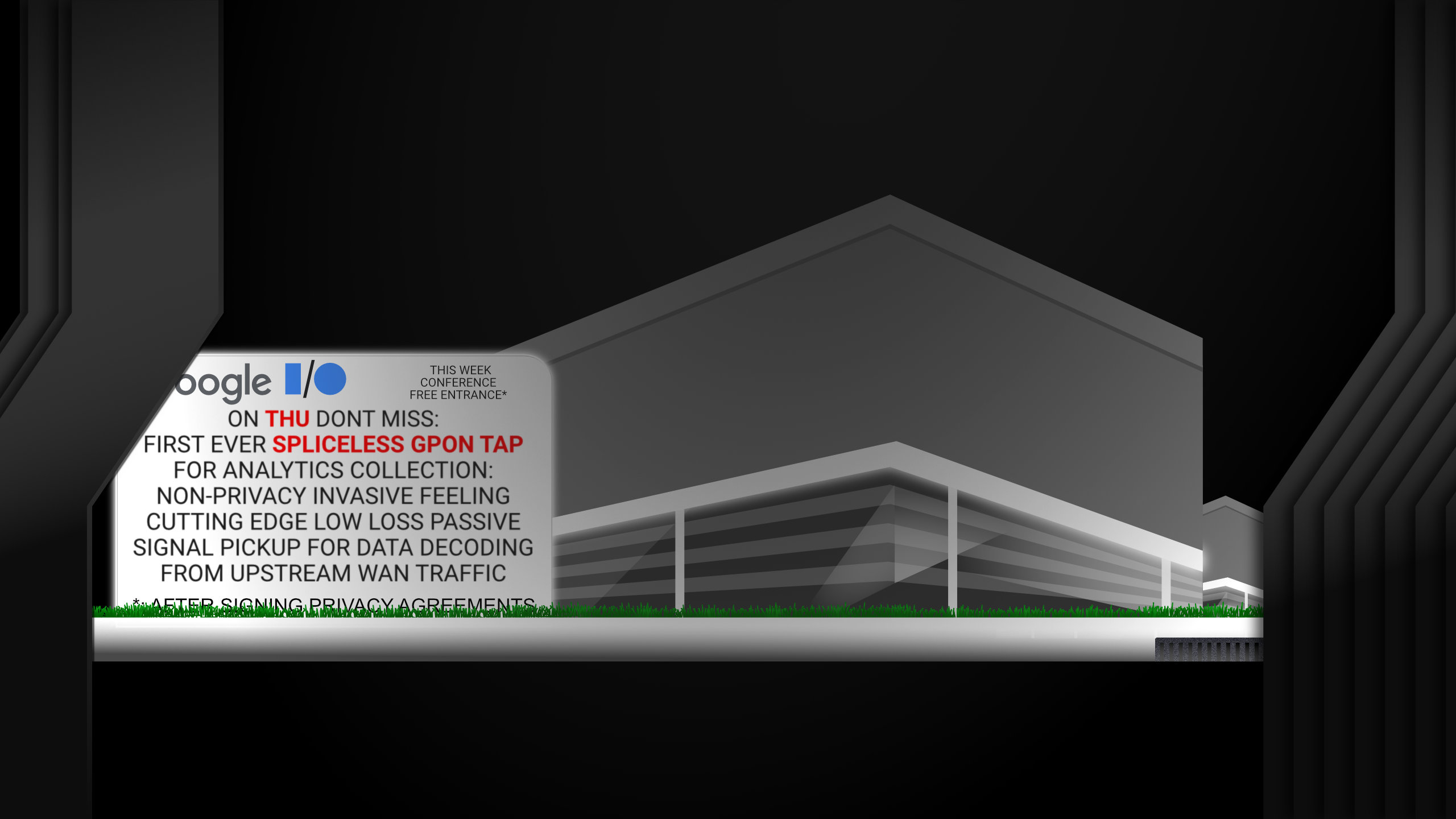
But you’ve heard all of this before. You probably become jaded to it. If so, then allow me to introduce you, or remind you about Federated Learning. One of those things I mentioned earlier.
What’s Federated Learning
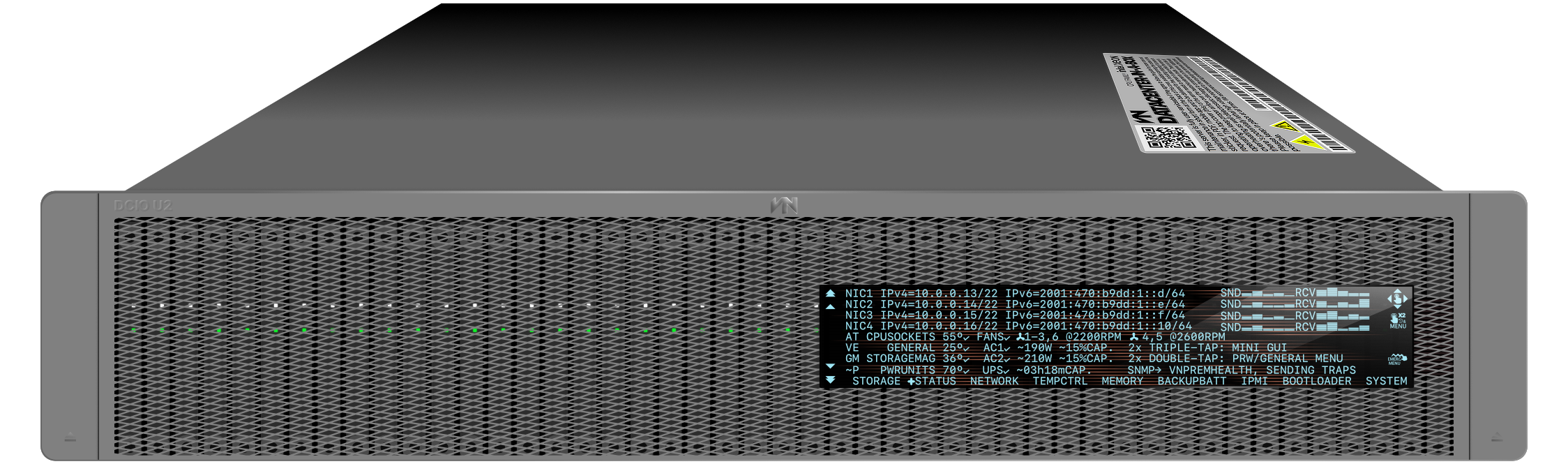
Basically, it’s offloading the compute needed for AI from Google’s data centers down to all Android users. Not your piece of the work, everybody’s or rather the work that Google has been advertising in their own Pixel devices with all of those powerful Tensorfuck AI chips or whatever, but really so far they had been sent to the data center for processing, costing the company money to offer this feature that I don’t personally know, or have heard of anybody that cares for it, wants it, or trusts it, yet regardless it’s still shoved down their throats, but now the work is done on-device. Whether you use it or not. Whether you want it or not.
After energy is wasted at your expense, the processed data is sent back to the cloud (gawd! I hate that term) for the “greater good” à la3 Folding@home, except that scratch the greater good because everybody can see and use and download the data of Folding@home whereas what Google has you process is completely encrypted, and most traffic transmitted to and from your devices nowadays; that encryption is not for your benefit. The federated meaning combined data “the learning” of it is not shared openly, unless of course you use Google’s products which happen to be good for its business given that they are its business. You know how logic can work in mysterious ways.
On second thought, what worked in mysterious ways might not be logic. Agh. Geography! Am I right? Who cares anyway, if you still don’t understand what I’m trying to say, what’s written in the title: Google is abusing you yet again, without your consent or tricking you to consent — which I’m convinced I am every time I’m forced to accept another EULA mid-service when a company is in a position to keep something hostage from you.
You should be angry about this. I know I am. I hate this. It’s the reason I can’t bring myself to use Windows and I’m still using a very discontinued macOS version. It’s not so much the data collection or the privacy implications which already should be non-negotiable absentees in a system but what irks me the most is the business behind it at your expense. The same goes for companies that sell you crowd-sourced data, specially live crowd-sourced data.
A sort of perfect example of this is antivirus software. I don’t know if you whre around of you remember how it used to work: you installed the thing which came with a preinstalled definitions list. Optionally you’d later update it with newer definitions lists which are the things used to identify viruses (yes, that is the plural) by the virus scanner. That’s not the case anymore, together with other malware-related (ransomware, intrusion prevention/protection, …), performance/efficiency/analysis-related (system, storage, sales, email), and the like that offer XaaS (what-fucking-ever as a service), you kind of are both their customer and their product but you are not compensated in either area. Not that it would make it okay.
Federation
In IT, federation tends to mean when standards are agreed upon to exchange information, the most common example are directory services and authentication/authorizations providers connections which might be a little much for most to understand, so an easier example is email (which coincidentally often — though feel free to read it as always — uses directory services for its user database — where users of one email service provider can exchange messages with users of another email service provider because it’s been agreed how shit should work. In other words, what protocols to use for the exchanging of the messages and all that.
However, federation also often used to loosely mean loosely interconnected, or siloed-but-you-can-still-get-to-it, or distributed. The last of which would apply much better in this case, but I can see how the use of that word would be slightly too transparent on the ulteriorness of its motives.
I know this kinda has a feel like a US’ Republican’s “why should my tax dollars {chest puff} fund the {thing4}” and then proceeding to pass short-sightedness, xenophobia, racism but more than anything selfishness as fairness5. This is not that kind of thing. You have earned the right to be furious about this especially if you are Americ— from the US where the most respected thing, the most important belief in life is money (and lawsuits but who’s counting, certainly not Google, that’s be or should be like a googol, and I can’t count past one hand because I need one free to mastur hold the mouse when I don’t have somebody to help me hold it and click it).
You are being robbed of your children’s innocence (I assume that amounts to money as well and children in a sentence is always good to stir some shit, late stage too, but I don’t know how to work it in). Grab that pitchfork and unite with your biggot-you-secretly-want-to-fuck6 of a neighbor and get up in arms, and with a little luck: down on fours; it’s bound to happen, you’ll be amped up, with a common enemy and of course drinking, because why not.
Google has a “cute” comic about this Federated Learning feature where it vaguely mentions the data sent is tiny, 5MB and the like, but so it’s Folding@home and if you put it and a powerful enough computer it will make your machine double as a furnace. I hear old Mac Pros can heat a whole room, the ones identical to PowerMacs.
In hindsight, I’ve said the same thing each time Google announces a new Pixel device, other than the Nexus 4 which at the time I think it was beautiful and I had to get on the gray market only to gift it away and the Pixel I own now which I chose only because it was the less hideous, I’m not a Pixel fan. So I’ve always had an ample supply of criticism at the ready. I try to be objective but I can’t deny that the fact that is a Google product and the company’s egregious behavior may at time cloud my judgment and has me on a constant high alert mode.
“Why do they keep packing in so much AI hardware bullshit in it if it still needs to connect to the Internet to do anything”.
It irked me that like I said before, they’re packing more and more power specifically for AI tasks, yet none of those features work offline.
“What’s the fucking point!? There’s always some connection to be made <<and since we’re here already, let’s dump all of this user personal information forgot I brought with me>>”
I had been missing the big picture. From the looks of it had been building the infrastructure right in our pockets, and it hasn’t stopped.
To Google’s credit, that’s actually very smart, and fucked up, and probably a low level engineer’s idea they got rid off before they could accrue some benefits and savvy7.
A redeemer
As I mentioned before, this is the Folding@home MO8 minus the goodwill; that Folding@home shares the product of the communal efforts. So I think the solution would be quite obvious, besides having some much fucking needed transparency or what leaves and comes into our devices, the data generated obtained by these methods should be made public for other organizations and individuals alike to use, even for profit because that’s what Google indirectly is doing, profiting from the advantage it might give it9.
Google may paint this resource-stealing endeavor as altruistic but it is everything but.